Securing Your Team’s Sensitive Presentations: Watermarking and Permission Control Guide

Your team’s most valuable presentations are also your biggest security risks. Client strategy decks contain competitive intelligence. Board presentations include unreleased financial data. Internal training materials reveal operational processes that competitors would love to see.
One leaked presentation can destroy deals, violate compliance requirements, or damage your company’s competitive position. But most teams treat presentation security as an afterthought. They email sensitive slides without encryption, share files with temporary contractors who keep access forever, and skip watermarking because it takes extra time.
This approach works until it doesn’t. Then you’re explaining to executives how confidential client data ended up in a competitor’s pitch deck or why regulatory documents are circulating without proper controls.
Executive Summary
The biggest risks come from mishandling presentations that contain competitive intelligence, client data, or regulatory information. Brand leaks damage relationships and competitive positioning. Unauthorized reuse dilutes your messaging and creates compliance problems. Poor permission management lets sensitive information reach unintended audiences.
Watermarking and permission controls aren’t just IT requirements. They’re business protection tools that preserve your competitive advantage and maintain client trust. The cost of implementing these controls is minimal compared to the damage from security breaches.
Understanding What Makes Presentations Sensitive
Not every presentation needs maximum security, but you need clear criteria for identifying sensitive content before problems occur.
Client pitches contain pricing strategies, competitive analysis, and relationship details that competitors would use against you. Confidential project data includes unreleased products, internal processes, and strategic decisions that affect market position. Regulatory presentations contain compliance information that requires specific handling and retention procedures.
Internal strategy decks reveal operational details, financial projections, and decision-making processes that could damage your position if disclosed publicly. Even routine training materials can contain sensitive information about processes, systems, or personnel.
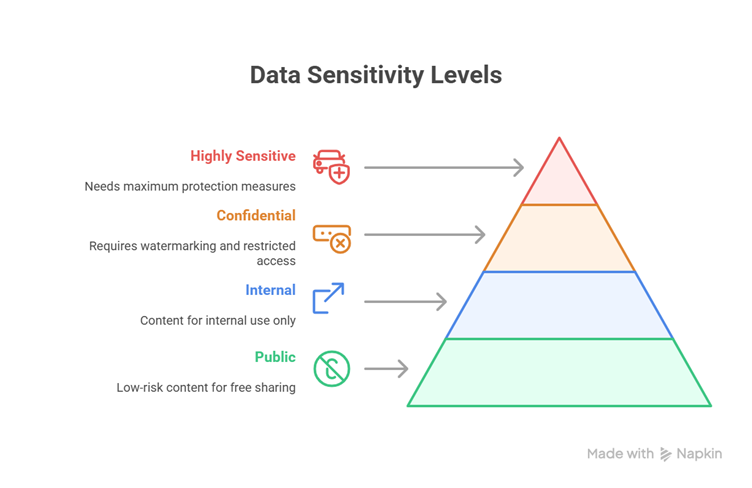
Create sensitivity levels that match your business risks. Level 1 might be public or low-risk content that can be shared freely. Level 2 covers internal content that shouldn’t leave the company but doesn’t require special controls. Level 3 includes confidential information that needs watermarking and restricted access. Level 4 covers highly sensitive content that requires maximum protection.
Part 1: Watermarking Your Presentations
Watermarking serves three purposes: deterring unauthorized distribution, communicating document status, and establishing ownership. Visible watermarks make people think twice before sharing inappropriately because they know the content is tracked.
Learn how to watermark your presentations here.
Types of Watermarks That Actually Work
Text watermarks work for most scenarios. “Confidential,” “Internal Use Only,” or “Draft” messages communicate document status clearly. Include your company name and date to establish ownership and version control.
Image watermarks using your logo reinforce branding while providing security identification. Make these semi-transparent so they don’t interfere with content readability but remain clearly visible.
Custom watermarks can identify specific projects, teams, or security levels. “Project Phoenix – Confidential” or “Sales Team Only” provides more specific access guidance than generic watermarks.
Implementation in PowerPoint and Google Slides
Use Slide Master to apply watermarks across entire presentations automatically. In PowerPoint, go to View > Slide Master, add your watermark text or image, then close Slide Master view. Every slide in the presentation gets the watermark without manual application.
Position watermarks where they’re visible but don’t interfere with content. Bottom corners or light backgrounds work well for text watermarks. Center positioning with high transparency works for logo watermarks.
For high-volume workflows, consider automation tools that apply watermarks to multiple presentations simultaneously. PowerPoint VBA scripts can watermark entire folders of presentations.
Limitations and Best Practices
Watermarks shouldn’t distract from your message or make text unreadable. Test watermark visibility across different projectors and screen types. What looks subtle on your monitor might be overwhelming when projected.
Maintain watermarked master templates separately from working presentations. When you need to remove watermarks for external sharing, work from clean masters rather than trying to remove watermarks from working files.
Remember that basic watermarks can be removed by determined users. They deter casual sharing and establish legal ownership but don’t provide technical protection against sophisticated removal attempts.
Part 2: Permission Controls and Access Management
Permission controls are your first line of defense against unauthorized access and sharing. They determine who can view, edit, or share your sensitive presentations.
Platform-Based Access Controls
Microsoft OneDrive and SharePoint provide granular access controls at both folder and file levels. You can assign Viewer rights for people who need to see content, Commenter rights for review workflows, and Editor rights for active contributors. These platforms also track access history and changes for audit purposes.
Google Drive offers similar functionality with real-time collaboration features. You can restrict downloading, printing, and copying for sensitive files. Share links can be set to expire automatically after specific time periods.
Both platforms integrate with your organization’s identity management systems, making it easier to manage access based on job roles and project assignments.
Advanced Protection Techniques
For highly sensitive presentations, consider additional protection layers. Password protection adds another barrier to unauthorized access. Document encryption protects files even if they’re downloaded to unsecured devices.
Expiring share links automatically revoke access after set time periods. This prevents long-term access for temporary collaborators like contractors or external consultants.
Third-party DRM solutions Adobe Experience Manager provide non-removable protection that persists even when files are downloaded. These solutions can prevent printing, screen capture, and watermark removal.
Governance Procedures That Work
Assign file and folder owners who maintain organization and security. These people review access permissions regularly, remove unnecessary access, and ensure security procedures are followed.
Monitor usage logs for unusual access patterns. Multiple downloads from unfamiliar locations, access outside normal business hours, or sharing with external domains might indicate security issues.
Establish regular access reviews, perhaps quarterly, to remove permissions for people who no longer need access. Staff changes, project completions, and role modifications all create opportunities for excessive access.
Part 3: Workflow Recommendations for Sensitive Presentations
Security procedures only work if your team follows them consistently. Build security into your normal workflow rather than treating it as an extra step.
Create team policies that specify how sensitive presentations should be handled. Define what constitutes sensitive content, what protection measures are required, and who has authority to share externally.
Train team members on watermarking and permission procedures during onboarding and provide refresher training when procedures change. Make security procedures part of project checklists rather than optional add-ons.
Establish communication procedures for updating master sensitive presentations. When confidential content changes, notify everyone who has access so they can update their local copies or delete outdated versions.
Develop emergency procedures for security breaches. If someone reports unauthorized sharing or potential leaks, your team needs to know how to revoke access, update affected presentations, and notify appropriate stakeholders quickly.
Implementation Roadmap
Start with your most sensitive presentations and expand coverage gradually. Trying to implement comprehensive security across all presentations simultaneously overwhelms your team and reduces compliance.
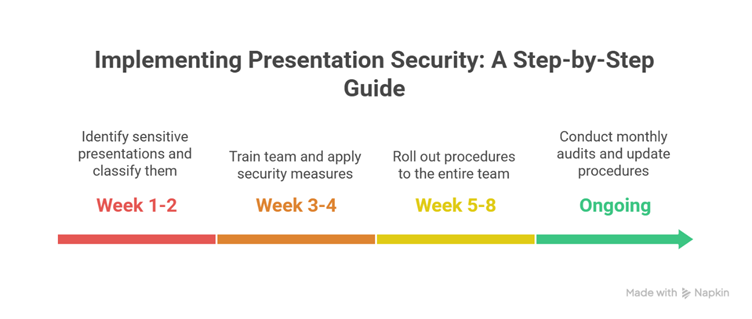
Week 1-2: Identify your most sensitive presentations and classify them by security level. Create watermarked master templates for high-sensitivity content. Set up permission controls for these critical files.
Week 3-4: Train core team members on security procedures and tools. Begin applying watermarks and access controls to existing sensitive presentations. Document procedures for future reference.
Week 5-8: Roll out security procedures to the entire presentation team. Monitor compliance and provide additional support where needed. Establish regular review procedures for ongoing maintenance.
Ongoing: Conduct monthly security audits, update procedures based on feedback, and expand security coverage to additional presentation types as team comfort increases.
Common Challenges and Solutions
Resistance to security procedures usually stems from perceived inconvenience or lack of understanding about risks. Address this by demonstrating real security incidents and showing how procedures prevent problems rather than just creating work.
Platform limitations can frustrate teams used to informal sharing. Work within your existing technology ecosystem rather than fighting it. If your team lives in Google Workspace, use Google Drive controls rather than forcing migration to different platforms.
Balancing security with productivity requires thoughtful procedure design. Security shouldn’t prevent legitimate work, but it should make unauthorized sharing more difficult. Focus on protecting your highest-risk content rather than applying maximum security to everything.
Making Security Sustainable
The best security procedures are the ones that happen automatically without constant management attention.
Build security into your presentation templates and folder structures. When security is baked into your tools, people don’t have to remember to add it later.
Make security status visible and easy to check. Teams should be able to quickly identify which presentations have appropriate protections and which need additional security measures.
Regularly review and update your security procedures based on changing business needs and threat environments. Security isn’t a one-time setup but an ongoing process that evolves with your team and industry.
Most importantly, remember that perfect security that prevents all work is worse than imperfect security that protects your most valuable assets while enabling productivity. Focus on protecting your highest-risk presentations with appropriate controls rather than trying to lock down everything equally.